
KI #1: The Tip of the Cyber Iceberg
On my first internship, managing risk and overcoming imposter syndrome
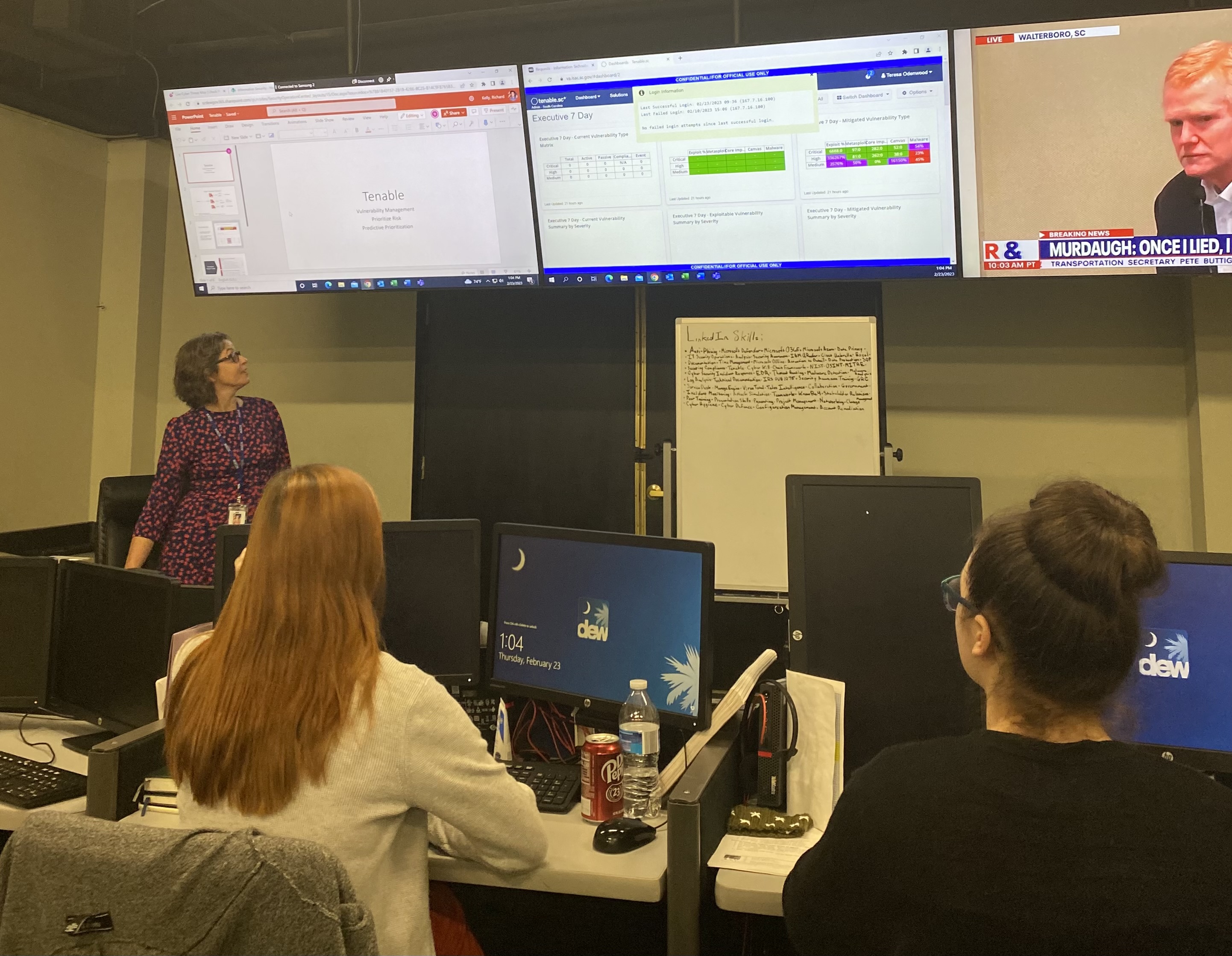
During my junior year matriculating at USC, something miraculous happened. I spent weeks that August applying to a myriad of computing internships, to no avail. Seeing as my mantra is “rejection is redirection”, I ceased the grueling application cycle and instead decided to dedicate my time to my role as then-program specialist at the Boys & Girls Club and to my Fall semester classes. On top of applying for jobs being an arduous task, narrowing down an internship for a career I sought proved futile, knowing little about what roles I wanted to pursue after graduation. Everything changed when a few weeks into September I received a phone call early one Friday morning. The Chief Information Officer (CIO) of the South Carolina Department of Employment and Workforce (DEW) had called me, and stated that I had been selected to participate in DEW’s inaugural cybersecurity analyst internship that had just launched in July as a member of the second cohort. Completely bewildered and elated that I had finally found an internship, I gladly accepted. Two weeks later, I found myself sitting through the orientation and onboarding process, terrified. Starting as an intern for a discipline I had limited knowledge in couldn’t have seemed like a worse idea. I felt I was doomed to fail, and the self-doubt rapidly set in– What if you make a mistake? What if you fail? What if you are not competent enough for the task at hand? Accepting this position had also meant accepting a huge amount of risk, so much so that I failed to recognize the reward. But I was completely unaware of how much knowledge I would accrue over the six-month duration of the program, nor the lifelong connections I would make along the way. This was done by putting the “what ifs” aside, and taking a stab at something new, and doing so has been one of the best decisions for my early career.
Going into my junior year, I had extraordinarily little knowledge of what I deem the “Cybersecurity Iceberg.” My program curriculum requires all CIS majors take CSCE 201 “Intro to Computer Security”, which covers basic security policies, incident response, risk management, basic cryptography and ends with students giving a presentation on the practice of security. As much as I enjoyed this class and its extremely talented lecturer Dr. Neema Kanapala, ingenuously, I did not realize just how deep this Iceberg was. While CSCE 201 introduced students to concepts like non-repudiation, encryption and common vulnerabilities, the topic of risk management is what stuck with me the most. Risk management in cybersecurity is similar to that of securing your digital world from bad things happening, much like you would lock your doors to keep your home safe. In class, we discussed the granularity of risk management, composed of identifying all assets a user has, identifying potential vulnerabilities of each asset, assessing the severity of each vulnerability, taking protective measures to secure the assets, monitoring all assets and preparing for the worst case scenario in the event of a breach. While the focal point of cyber risk management is identifying potential problems and taking steps to preempt them, my exposure to risk management frameworks (RMF) did more for me than merely adjusting my thinking to sleuth weaknesses in my firm’s information systems. As someone that suffered from imposter syndrome in my sector, choosing a career field had left me feeling anxious and completely unqualified for the roles I perused. This change in mindset that I had applied in class and later in the workforce edified my confidence in the field as a whole. The skills and logic I developed in learning textbook risk management on covering all my bases easily translated to me asking myself “What steps can I take to feel comfortable with this material?”

According to numerous research studies, including medium.com, 58% of employees in tech suffer from imposter syndrome more frequently than those that are not. I served as no exception to those statistics. My first two months into the internship were stress-inducing, as interns were not trained through simulation-based training. Instead, everything we did was on the live network– meaning that in responding to a ticket, clicking on a malicious URL would actually trigger a breach to a local government agency. I cannot help but reminisce on the immense risk in coming to work in this role. On the live network, a security breach could have occurred at any day, whether it be from threat actors penetrating the system, or an intern misclicking a malicious link and forfeiting login credentials. Miraculously, no intern ever caused a data breach! My allurement for the tech sector has in part been my fascination with cybersecurity and underlying network protocols that makeup our internet. Pivoting into computer science is certainly the best decision I’ve ever made for my career, but even burning desire to contribute to a field failed to thwart my anxiety that I was not capable of thriving in tech. Uneasiness on what computing niche to pursue with my degree was finally alleviated by this internship, where I faced risk mitigation and management situations everyday in the form of helpdesk tickets. This experience has led to my certainty that I want to continue expanding my cybersecurity expertise, and bridge it closely to other computing disciplines.
No matter, the pipeline from taking an area of my studies that I had superficial knowledge in and applying it every day for six-months did wonders not only for my proficiency on the subject-matter, but helped me build confidence in problem-solving security queries in real-time, further bridging what I had gleaned in my concurrent classes those two semesters. Since my completion of the program, I improved my investigation time requirements by 150%, performed log-source reviews and developed the first agency-wide phishing attack simulation with my workfellow. Getting into the routine and establishing familiarities with the workload and frameworks was most beneficial in tackling my imposter syndrome. My key takeaway to vanquishing the syndrome was gaining confidence in my understanding of the material and being able to talk about my various roles with both people within and out of the cyber sector. Of course, imposter syndrome in a computing field can never truly be vanquished, but the understanding that the field is always evolving and transforming makes it a fun challenge to keep up. None of these projects would have been possible without the patience, guidance and opportunity provided by DEW and our CIO, Shane Simmons, who arranged the entire program. Not only do I plan to apply the invaluable knowledge I gained to all tech positions I land going forward, but I will continue to develop fluency in infosec, as cybersecurity is ubiquitous. Even as I write this, I am studying for CompTIA’s Security+ certification exam, which denotes proficiency in security baselines.
While my internship ended in March 2023, things have come full circle this semester, as I am currently taking CSCE 522 Information Security Principles, only further reinforcing the cybersecurity concepts I practiced daily during the program. This surreal experience has no doubt bettered me as a CIS student at USC. It astounds me that the introduction to a simple concept like threat analysis provided me so much clarity and will only strengthen my decision-making and judgment going forth. I am ecstatic to share my newfound affinity for cybersecurity with like-minded individuals and to enterprises in need. Though I am stricken by nostalgia for how much character growth I made during my time at the program, looking forward, I am so grateful for being selected as a participant. In retrospect, I can say that the cybersecurity concepts I practiced do not end at data security and securement of information systems, but catalyzed the manner in which my imposter syndrome was surmounted.
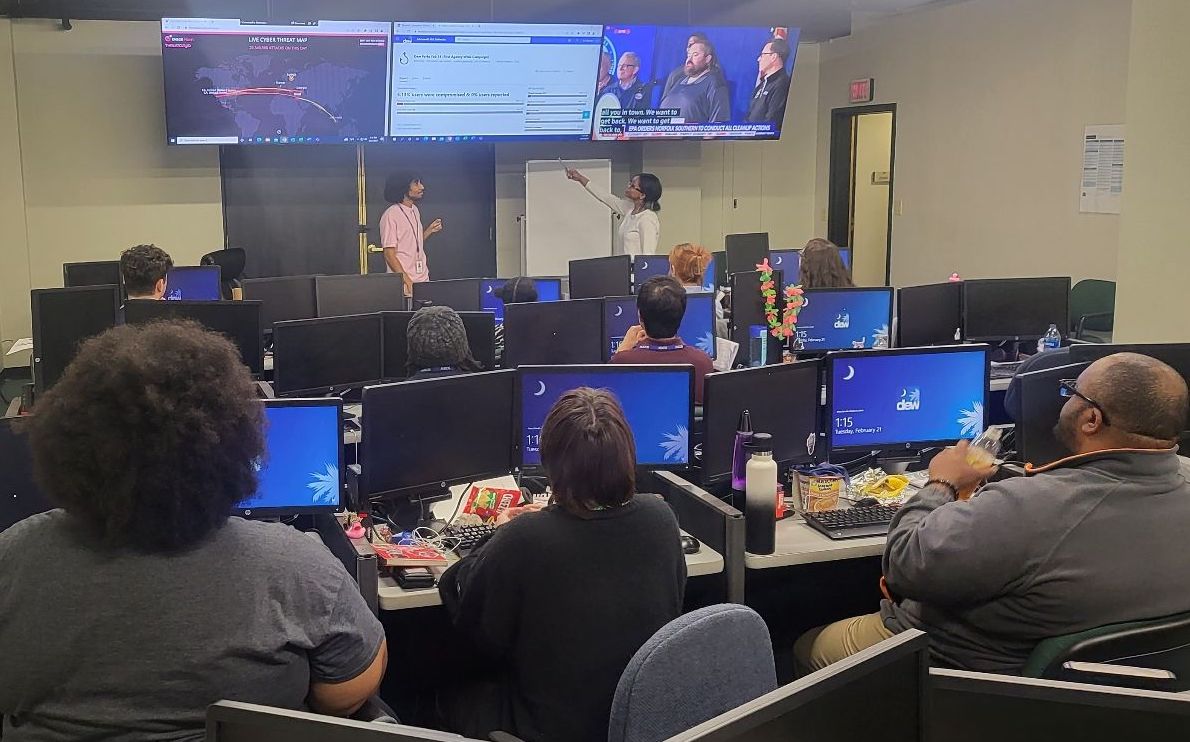
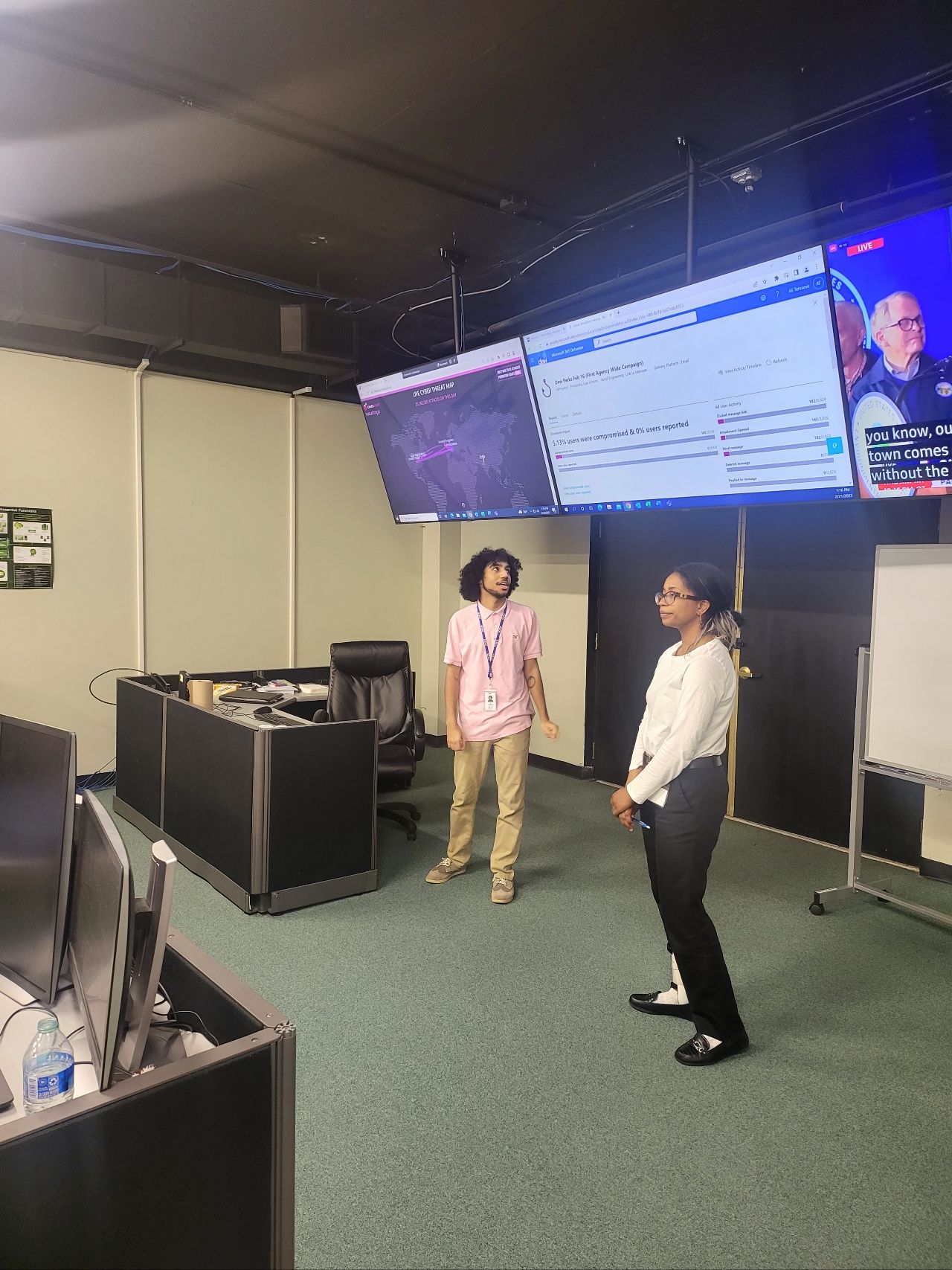
 Attack Simulation After Action Report
Attack Simulation After Action Report